Leading Cyber Security in a Hyperconnected World
Evolving Mental Models for an Uncertain Future
Executive Summary
The digital transformation of human civilisation has created unprecedented complexity in how we work, communicate, govern, and innovate. Cyber security has evolved from a technical specialisation to the foundational infrastructure enabling this transformation. Yet the cognitive frameworks security leaders employ to navigate this complexity have not kept pace with the challenges they face.
This paper establishes the case for structured mental models in security leadership and introduces the CISO Mental Model — a comprehensive framework purpose-built for the unique demands of 21st century information security leadership in an increasingly digital-first world.
Part I: The Evolution of Human Problem-Solving
The Foundations of Structured Reasoning
Human progress hinges on our capacity to reason through complexity and solve novel problems. Yet reasoning rarely occurs in a vacuum. It relies on underlying frameworks that shape how we perceive problems, evaluate evidence, and generate solutions. These frameworks, known as mental models, function as cognitive tools that either amplify or constrain our problem-solving capabilities.
Throughout history, philosophers and scientists have recognised that effective reasoning requires structure. Aristotle's syllogistic logic provided the first formal system for deductive reasoning. If all men are mortal, and Socrates is a man, then Socrates is mortal. This framework dominated logical thought for centuries, offering a reliable method for deriving valid conclusions from accepted premises.
The Scientific Method, crystallised during the Enlightenment, introduced systematic empirical reasoning. Francis Bacon's inductive approach — observing particulars to derive general principles — complemented deductive logic. This mental model transformed problem-solving by establishing protocols: hypothesise, test, observe, refine. Its power lies not merely in its steps, but in its underlying model of how knowledge accumulates through iterative learning.
Yet formal logic and scientific method, whilst powerful, proved insufficient for many real-world challenges where problems are ill-defined, information incomplete, and trade-offs inevitable. The complexity of modern organisational, technological, and social systems demands additional cognitive frameworks.
Mental Models as Cognitive Accelerators
Mental models serve as reasoning shortcuts that compress experience and expertise into applicable patterns. They help us recognise problem types, predict consequences, and identify leverage points. Unlike simple heuristics that provide quick answers, mental models provide structured ways of thinking about problems that reveal non-obvious relationships and second-order effects.
The most powerful mental models share several characteristics.
Generalisability means they apply across domains. Systems thinking works whether analysing ecosystems, organisations, or software architectures.
Transferability allows experts to teach them explicitly, enabling others to apply accumulated wisdom without repeating all experiences.
Cognitive efficiency reduces mental load by providing ready frameworks, freeing attention for novel aspects of problems.
Error correction reveals when our intuitions mislead us, preventing systematic reasoning failures.
Part II: Essential Mental Models for Complex Problem-Solving
Modern problem-solving demands a repertoire of complementary mental models, each suited to different types of complexity.
Systems Thinking: Understanding Interconnection
Systems Thinking addresses problems where causes and effects intertwine through feedback loops, time delays, and emergent properties. It recognises that systems exhibit behaviours their components cannot. Organisational culture isn't reducible to individual beliefs, market dynamics exceed any trader's intentions, and security posture emerges from interactions across people, process, and technology.
In cyber security, a vulnerability isn't merely a technical flaw. It exists within an ecosystem of threat actors, defensive measures, human behaviour, and organisational culture. Systems thinking reveals why patching individual vulnerabilities whilst ignoring systemic weaknesses resembles repairing individual rust spots whilst the entire structure corrodes. The vulnerability reappears because the system producing vulnerabilities remains intact.
Systems thinking provides conceptual tools. Feedback loops show where actions reinforce or balance themselves. Delays reveal where causes and effects separate temporally, obscuring relationships. Stocks and flows demonstrate where accumulations matter as much as rates. These concepts enable reasoning about dynamics that linear thinking misses.
Probabilistic Thinking: Reasoning Under Uncertainty
Probabilistic Thinking replaces binary certainty with likelihood assessments. Rather than asking "will this risk materialise", it asks "what probability should we assign, and what's the expected value". This model, fundamental to Bayesian reasoning, enables better decisions under uncertainty.
Risk managers employ probabilistic thinking when allocating resources across multiple threats with varying probabilities and impacts. A high-probability, low-impact risk might warrant more attention than a low-probability, catastrophic risk — or vice versa — depending on risk tolerance and available mitigations. The model forces explicit reasoning about uncertainty rather than treating unknowns as knowns.
Bayesian updating provides the mathematical foundation. As new evidence arrives, update probability estimates systematically. If threat intelligence suggests increased targeting of your sector, update the probability assessment for relevant attack scenarios accordingly. This prevents both premature certainty and paralysis in the face of uncertainty.
Second-Order Thinking: Anticipating Consequences of Consequences
Second-Order Thinking extends reasoning beyond immediate consequences to downstream effects. Every action triggers chains of effects, and the second-, third-, and nth-order consequences often dominate outcomes.
Mandating complex password requirements provides clear first-order effects — improved password entropy reduces vulnerability to dictionary attacks. But second-order thinking reveals additional consequences. Password reuse across systems occurs because users cannot remember unique complex passwords. Written passwords appear under keyboards or in unsecured notes files. Help desk burden increases from forgotten passwords. User frustration reduces security culture. The second-order effects may overwhelm the first-order benefits.
Second-order thinking prevents solutions that solve one problem whilst creating larger ones. It forces questions: and then what happens? What does this enable or prevent? What changes when everyone adapts to this? Strategic decisions particularly demand second-order thinking, as their consequences unfold over years through complex social and organisational dynamics.
Inversion: Attacking Problems Backwards
Inversion attacks problems from the opposite direction. Rather than "how do we achieve resilience", ask "what would make us maximally fragile". This reveals hidden assumptions and non-obvious failure modes.
The mathematician Carl Jacobi famously advised "invert, always invert". In corporate governance, inverting the question exposes single points of failure that forward-reasoning might miss. What would cause our incident response to fail catastrophically? Lack of executive authority, unclear ownership, untested procedures, degraded communication during stress, dependencies on unavailable personnel. Identifying fragility sources enables targeted strengthening.
Inversion complements direct problem-solving. Some problems yield more readily to identifying and removing failure modes than to directly constructing success. In complex systems, removing negatives — single points of failure, known vulnerabilities, process bottlenecks — often proves more tractable than optimising positives.
First Principles Thinking: Reasoning from Fundamentals
First Principles Thinking strips problems to foundational truths, rebuilding understanding from the ground up rather than reasoning by analogy. This model breaks free from "how it's always been done" constraints.
Elon Musk's approach to battery costs demonstrates first principles thinking. Rather than accepting industry benchmarks, he examined raw material costs — cobalt, nickel, lithium, carbon, polymers for separators — and manufacturing processes. Calculating costs from constituent materials revealed batteries could theoretically cost a fraction of prevailing prices if manufactured efficiently. This insight, unavailable through analogical reasoning, enabled breakthrough approaches.
In security, first principles thinking questions inherited assumptions. Why do we structure security functions this way? What problem does this control actually solve? What's the minimum necessary to achieve the security outcome? This reasoning mode proves particularly valuable when entering new domains — cloud security, IoT security, AI security — where direct analogies mislead.
Occam's Razor: Favouring Simplicity
Occam's Razor favours simpler explanations over complex ones when evidence equally supports both. In troubleshooting, this prevents over-engineered solutions and conspiracy theories when mundane explanations suffice.
The principle doesn't assert that simpler explanations are always correct. It asserts that absent differentiating evidence, simpler explanations should receive preference. They make fewer assumptions, thus fewer points of potential failure. A system outage is more likely caused by a misconfigured firewall rule than a sophisticated nation-state attack, though both could produce similar symptoms.
Occam's Razor provides heuristic value. Start investigations with simpler hypotheses, moving to complex explanations only when evidence demands them. This saves cognitive resources and prevents the complexity bias — our tendency to attribute events to complicated causes even when simple explanations suffice.
The Integrated Reasoner: Model Selection and Application
Effective problem-solvers maintain a repertoire of mental models, selecting contextually appropriate frameworks. A cyber security incident might require systems thinking to understand how the attack propagated through interconnected systems, probabilistic thinking to prioritise response actions under uncertainty, second-order thinking to evaluate whether containment measures create new vulnerabilities, inversion to stress-test defensive assumptions, first principles to question inherited response protocols, and Occam's Razor to avoid over-complicating attribution.
The meta-skill isn't mastering individual models but recognising which problems require which frameworks, and when our current models fail us — signalling the need for new ones. Charlie Munger, Warren Buffett's long-time partner, advocated for a "latticework of mental models", arguing that problems sitting at disciplinary intersections require drawing on multiple models simultaneously.
Part III: The 21st Century Context — Digital Transformation and Cyber Primacy
The Digital-First Civilisation
We inhabit a civilisation undergoing fundamental transformation from physical-first to digital-first in nearly every domain of human activity. This transition represents more than technological change — it constitutes a phase shift in how humans organise collective action, create value, and structure society.
Economic Activity sees global GDP increasingly derive from digital products, services, and platforms. Physical goods carry digital components. Cars are software platforms, manufacturing comprises cyber-physical systems, agriculture employs sensor networks and AI-driven analytics. The distinction between "technology companies" and other organisations collapses as all enterprises become technology-enabled.
Social Infrastructure operates predominantly through digital channels for human communication, relationship formation, and social coordination. Political movements organise via social media. Communities form around digital platforms transcending geography. Cultural production and consumption shift to streaming, social media, and digital marketplaces.
Governance and Services now deliver digitally. Telemedicine, online education, digital identity all function through cyber infrastructure. Governments conduct surveillance via cyber means and face threats to critical infrastructure through cyberspace. Democracy itself confronts challenges from digital disinformation, algorithmic polarisation, and cyber-enabled authoritarian control.
Knowledge and Innovation depend on computational modelling, big data analysis, and digital collaboration. AI systems increasingly augment or automate cognitive work. Human knowledge itself resides primarily in digital form, vulnerable to cyber disruption.
This digital transformation creates unprecedented dependencies. A sophisticated civilisation running on digital infrastructure faces existential risks from cyber disruption. The 2021 Colonial Pipeline ransomware attack, which disrupted fuel supplies across the U.S. East Coast, illustrates how cyber incidents can cascade into physical-world consequences affecting millions.
The Scale of Digital Dependence: Market Capitalisation vs GDP
The digital transformation manifests in concrete economic realities revealed through a striking metric. The ratio of stock market capitalisation to gross domestic product shows something remarkable. When corporate market value approaches or exceeds national economic output, we observe unprecedented concentration of value in organisations whose operations depend fundamentally on cyber infrastructure.
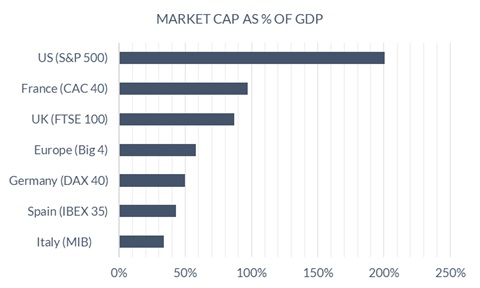
United Kingdom presents a clear example. The FTSE 100 commands a combined market capitalisation of $2.98 trillion against the UK's GDP of $3.42 trillion, representing 87% of the national economy. This means that fewer than 100 corporations account for over two-thirds of Britain's entire economic value. Each of these entities depends entirely on cyber infrastructure for operations spanning global supply chains, digital commerce, financial transactions, and data-driven decision-making.
United States shows the concentration more extremely in the world's largest economy. The S&P 500 index carries a combined market capitalisation of $58.56 trillion — two hundred percent of U.S. GDP of $29.18 trillion. American corporate market value doesn't merely match the national economy; it doubles it. This extraordinary ratio reflects both the global reach of U.S. corporations and premium valuations driven by expectations of continued digital innovation. The implication is clear: a cyber disruption affecting major S&P 500 companies threatens economic value exceeding the entire annual output of the American economy.
Mainland Europe continues the pattern across major economies, though with notable variation. Examining the "Big Four" European economies reveals the following.
| Economy | Index | Market Cap | GDP | Ratio |
|---|---|---|---|---|
| France | CAC 40 | $3.08 trillion | $3.18 trillion | 97% |
| Germany | DAX 40 | $2.40 trillion | $4.85 trillion | 50% |
| Spain | IBEX 35 | $0.72 trillion | $1.68 trillion | 42% |
| Italy | FTSE MIB | $0.79 trillion | $2.33 trillion | 34% |
| Combined | $6.99 trillion | $12.04 trillion | ~58% |
The variation across European nations — from Italy's 34% to France's 97% — reflects different stages of digital transformation, market development, and corporate concentration, but all depend fundamentally on cyber infrastructure.
Cross-Regional Patterns and Implications
Three patterns emerge from these figures.
Value Concentration shows that in advanced economies, corporate market value represents 58–87% of GDP in mainland Europe and the UK, or vastly exceeds it in the US at 200%. This isn't merely corporate success — it represents structural dependence. Modern economies function through corporations whose operations require cyber infrastructure.
Unprecedented Scale appears in the S&P 500's market capitalisation exceeding GDP by 2 to 1, which has no historical precedent. Medieval trade, industrial manufacturing, even early computing never concentrated value at this scale in entities depending on a single foundational infrastructure whose failure cascades systemically.
Systemic Interdependence operates because these corporations don't function independently. They form interconnected ecosystems. Supply chains link manufacturers across continents. Financial systems enable capital flows between entities. Cloud platforms host multiple competitors' operations. A cyber incident affecting one major corporation cascades through business relationships, supply dependencies, and financial interconnections.
Security Leadership at GDP-Relevant Scale
These numbers transform security leadership from corporate function to economic stewardship. A successful cyberattack on a major S&P 500 company doesn't merely affect that entity — it potentially disrupts a portion of the $58.56 trillion in market value those 500 companies represent. When the Colonial Pipeline ransomware attack occurred in 2021, a single company's compromise disrupted fuel supplies across the U.S. East Coast, demonstrating how cyber incidents translate into physical-world consequences affecting millions.
A FTSE 100 CISO doesn't just protect one company among Britain's 100 largest. They safeguard roughly 1% of the UK's total corporate value — approximately $30 billion average market cap per FTSE 100 company. Their decisions about architecture, resilience, and risk acceptance carry consequences at national economic scale.
When France's CAC 40 companies command market value approaching the entire French economy at 97%, security leaders in those organisations function as guardians of economic infrastructure, not merely corporate IT managers.
The concentration of economic value in digitally-dependent corporations, combined with systemic interconnections between them, creates a security challenge without historical precedent. This is why mental models for security leadership matter at civilisational scale. The cognitive frameworks CISOs employ influence economic systems supporting billions of people's livelihoods and trillions in economic value.
Cyber Security as Foundational Infrastructure
In this context, cyber security evolves from a technical specialisation to foundational infrastructure enabling continued human progress. Just as physical security — rule of law, property rights, borders — enabled agricultural and industrial civilisation, cyber security enables digital civilisation.
This elevation changes what security leadership demands. Early information security focused on protecting specific assets: databases, networks, endpoints. Contemporary security must protect entire digital ecosystems whilst enabling the innovation and openness that digital civilisation requires. The challenge combines technical sophistication with strategic thinking, risk management with business enablement, and individual expertise with organisational capability.
The Complexity Challenge for Security Leaders
The Chief Information Security Officer role crystallises these pressures. CISOs must simultaneously manage operational security, navigate strategic uncertainty, balance competing demands, communicate across contexts, build organisational capability, and deliver under resource constraints.
Manage Operational Security means detect and respond to threats daily whilst maintaining defensive infrastructure across increasingly complex, distributed environments — cloud, mobile, IoT, operational technology.
Navigate Strategic Uncertainty requires anticipating emerging threats — quantum computing, AI-enabled attacks, supply chain compromises — whilst building resilience against unknown unknowns.
Balance Competing Demands involves enabling business innovation and agility whilst maintaining appropriate security controls. Overly restrictive security stifles the digital capabilities organisations need to compete; inadequate security exposes organisations to devastating breaches.
Communicate Across Contexts requires explaining technical risks to non-technical executives, translating business requirements into security controls, and coordinating across diverse stakeholders — board, C-suite, technical teams, business units, regulators, customers, and partners.
Build Organisational Capability means developing security talent in a supply-constrained market, creating security culture amongst employees with varying technical sophistication, and embedding security throughout organisational processes.
Deliver Under Resource Constraints demands accomplishing all of this with finite budget, limited personnel, and perpetual pressure to do more with less.
This multidimensional challenge exceeds human cognitive capacity without structured frameworks. A CISO trying to hold all these concerns simultaneously in working memory will experience cognitive overload, leading to reactive decision-making, domain blindness, and strategic drift.
Part IV: The Case for Domain-Specific Mental Models
Why General Mental Models Prove Insufficient
The mental models discussed earlier — systems thinking, probabilistic reasoning, inversion, first principles — provide essential cognitive tools. A CISO employing these models will reason more effectively than one who doesn't.
Yet general-purpose mental models, whilst necessary, prove insufficient for the specific complexity of security leadership. They offer thinking frameworks but not domain structure. They help reason about problems once identified but don't ensure comprehensive problem identification. They enable good decisions within scope but don't define appropriate scope.
Consider systems thinking applied to security. It reveals that security incidents result from complex interactions, not isolated causes. It suggests examining feedback loops, delays, and emergence. But it doesn't specify which systems matter most, how to prioritise attention across different systemic risks, or what constitutes the relevant system boundary for security leadership.
Domain-specific mental models complement general reasoning frameworks by providing structured understanding of specific problem domains. In medicine, diagnostic frameworks help physicians reason systematically about symptoms, differential diagnoses, and treatment options. In software engineering, design patterns provide proven solutions to recurring problems. In finance, valuation models structure thinking about asset worth.
Security leadership demands its own domain-specific mental model — one that structures the multidimensional complexity inherent to the CISO role.
Requirements for a CISO-Specific Mental Model
An effective mental model for CISO leadership must satisfy several requirements.
Comprehensiveness means covering the complete scope of security leadership, not merely technical security or risk management or governance in isolation.
Structured Decomposition requires breaking overwhelming complexity into manageable domains whilst preserving understanding of interactions between domains.
Actionability provides concrete guidance for capability assessment, priority-setting, and development planning — not merely conceptual understanding.
Scalability allows application to organisations of varying sizes and maturity levels, from startups to multinational enterprises.
Adaptability ensures relevance as technology, threats, and business context evolve rather than encoding time-bound specifics.
Communicability enables clear explanation to different stakeholders — board members, executives, technical teams, peers — who need to understand security leadership.
Practitioner Validation emerges from actual operating environment experience rather than pure theory, capturing tacit knowledge that distinguishes effective from ineffective security leadership.
Part V: The CISO Mental Model — Structure and Function
Overview: Six Domains of Security Leadership
The CISO Mental Model structures security leadership responsibilities into six interconnected domains, each representing a distinct dimension requiring different thinking approaches, skills, and organisational capabilities.
The six domains are Governance, People Management, Strategy and Planning, Security Architecture, Security Engineering, and Security Operations.
Governance establishes the control plane through which security operates as a managed, accountable capability.
People Management builds and sustains the human capital that delivers security outcomes.
Strategy and Planning positions security for future success whilst managing present constraints.
Security Architecture designs security capabilities into infrastructure rather than retrofitting.
Security Engineering translates architectural intent into implemented, operating systems.
Security Operations maintains security posture through daily operational rhythm.
These domains aren't arbitrary categories but represent fundamental aspects of security leadership that demand sustained attention. Neglecting any domain creates systemic weaknesses that adversaries or operational failures will exploit.
The Model as Cognitive Framework
The CISO Mental Model functions as a mental framework in several ways.
Attention Direction ensures leaders maintain awareness across all critical domains rather than fixating on comfortable areas whilst others deteriorate. Many CISOs naturally gravitate toward technical domains — Architecture, Engineering, Operations — whilst underinvesting in Governance, People, or Strategy. The model corrects this bias through explicit domain identification.
Pattern Recognition enables identification of similar problems across different contexts. A capability gap in monitoring and triage shares structural similarities with capability gaps in architectural review. Both require systematic processes, clear ownership, and regular execution. Recognising the pattern enables transferring solutions.
Communication Framework provides shared language for discussing security leadership with different stakeholders. Board members care primarily about Governance and Strategy domains. Technical teams focus on Architecture, Engineering, and Operations. HR partners need to understand People Management. The model enables tailoring communication to audience whilst maintaining a coherent overall narrative.
Assessment and Planning structures capability maturity assessment, enabling systematic evaluation of current state, identification of gaps, and prioritisation of development initiatives. Without such structure, assessments become either superficial — checking boxes — or overwhelming, attempting to evaluate everything simultaneously.
Systems Understanding reveals critical interdependencies between domains. Strategy without People capability produces unfulfilled plans. Architecture without Engineering remains theoretical. Operations without Governance becomes chaotic firefighting. Understanding these interdependencies prevents locally optimal decisions that create systemic problems.
Domain Overview: Governance
Governance establishes how security operates as a managed, accountable capability rather than ad-hoc technical activities. This domain encompasses programme management — strategic and tactical — multi-directional reporting, compliance management, people and financial management integration, risk and control frameworks, and executive and operations committees providing decision-making forums.
Effective governance prevents common failure modes: invisible security work that leadership doesn't understand or value; reactive firefighting without strategic direction; compliance treated as checklist rather than risk management; security decisions made without appropriate organisational input or accountability.
The governance domain provides the organisational infrastructure enabling all other domains to function effectively. Without governance, even technically sophisticated security organisations struggle to deliver consistent results or maintain leadership confidence.
Domain Overview: People Management
People Management addresses the reality that security capability ultimately resides in people, not technology or processes. This domain covers performance management, development programmes, and succession planning — creating resilience against key person dependencies.
Elevating People Management to domain-level status reflects that human capital requires different management approaches than technical or financial capital. Security work demands expertise taking years to develop, occurs in a supply-constrained talent market, and requires continuous learning as threats and technology evolve.
Organisations that underinvest in People Management experience predictable problems. High attrition destroys institutional knowledge. Capability gaps constrain strategy. Burnout from unsustainable operational pressure becomes endemic. Strong People Management converts individuals into effective teams and creates organisational capability that survives personnel changes.
Domain Overview: Strategy and Planning
Strategy and Planning addresses how security positions itself for future success whilst managing present constraints. This domain encompasses resource planning, cyber risk categorisation, strategic resilience planning, control management, continuous improvement, stakeholder relations, and financial synchronisation.
The Strategy domain tackles the perpetual tension between immediate operational demands and longer-term capability development, between finite resources and expanding scope. Without strategic discipline, security organisations consume all resources managing today's problems whilst tomorrow's threats develop unchecked.
Strategic resilience planning exemplifies this domain's importance. Organisations must determine acceptable impact levels, recovery time objectives, and resilience investment priorities based on business context. These are decisions with multi-year implications that cascade through Architecture, Engineering, and Operations.
Domain Overview: Security Architecture
Security Architecture addresses how security capabilities get designed into infrastructure rather than bolted on afterward. This domain operates at two distinct levels. Specialist domain architecture provides detailed technical guidance for configuration management, endpoint security, network security, data security, secure development, identity management, and resilience patterns. Enterprise architecture ensures coherence through frameworks, reviews, and policy development.
Architecture determines what gets built, and what gets built determines what can be secured. Poor architecture cannot be rescued by excellent engineering or operations. Well-executed architecture enables effective security at sustainable operational cost.
Domain Overview: Security Engineering
Security Engineering translates architectural intent into implemented, operating capability. Where architecture defines what should exist, engineering builds it. This domain addresses data protection implementation, endpoint protection across diverse device types, connectivity engineering, and secure development lifecycle integration.
Engineering represents the craft of security implementation. Attention to detail, testing rigour, operational considerations, and trade-off management convert specifications into systems functioning effectively in production. Poorly-implemented good architecture delivers worse outcomes than well-implemented elementary architecture.
The distinction between Architecture and Engineering prevents common failure modes where either brilliant architectural visions never materialise — lack of engineering discipline — or implementation excellence produces inconsistent results — lack of architectural coherence.
Domain Overview: Security Operations
Security Operations represents the daily operational rhythm maintaining security posture, detecting threats, responding to incidents, and ensuring designed-and-built capabilities continue functioning effectively. This domain encompasses identity and access management operations, monitoring and triage, infrastructure maintenance, threat management, vulnerability management, incident response and digital forensics, and resilience operations.
Within Operations sit three substantial capabilities that could have been elevated to separate domains: vulnerability management, incident response and digital forensics, and resilience operations. Their positioning within Operations reflects that whilst strategically important, they manifest fundamentally as operational capabilities requiring continuous operational execution.
Operations is where all other security investments prove their value through actual defence against real threats. Without effective operations, governance remains theoretical, architecture stays on paper, engineering delivers unused capabilities, and strategy produces unfulfilled plans.
The System, Not Checklist: Understanding Interdependencies
The model's power lies not in individual domains but in their interactions. Resilience exemplifies these interdependencies. Strategic resilience requirements drive architectural patterns, which engineering implements, which operations executes daily. Each domain plays its distinct role in complete resilience capability.
Similar interdependencies exist throughout the model. Governance enables all other domains through programme structures and decision forums. People capability determines how effectively other domains can function. Strategy provides direction that Architecture and Engineering execute. Operations provides feedback that refines Strategy, Architecture, and Engineering.
Understanding these interdependencies prevents common failure modes: over-investing in some domains whilst neglecting others creates systemic weaknesses at the weakest point; making domain decisions without considering impacts on other domains leads to local optimisations creating global problems; treating domain boundaries as barriers rather than interfaces requiring careful management undermines effectiveness.
Part VI: Application and Value Creation
How Security Leaders Use the Mental Model
The CISO Mental Model serves multiple practical purposes.
Strategic Planning enables systematic capability assessment across all domains that reveals gaps and enables prioritised investment. Rather than ad-hoc decisions about where to strengthen security, leaders can evaluate maturity across domains, identify the weakest links creating most risk, and develop balanced improvement programmes.
Operational Awareness through regular reflection using the framework prevents domain blindness. Leaders can ask systematically which domain they're neglecting, where their attention has focused whilst other areas deteriorated, and whether they're maintaining appropriate balance.
Communication and Stakeholder Management recognises that different stakeholders care about different domains. Board members focus on Governance and Strategy. Technical teams emphasise Architecture, Engineering, and Operations. HR partners need People Management understanding. The model enables tailoring communication to audience whilst maintaining a coherent overall narrative.
Team Development and Delegation uses the model to provide structure for distributing leadership across the security organisation. Rather than the CISO attempting to own all domains personally, domains can have designated owners who develop domain expertise and maintain domain health. This distributes cognitive load and develops leadership bench strength.
Problem Diagnosis applies the model when security issues arise to help identify root causes. Is this an Operations failure, an Engineering problem, an Architecture gap, a Strategy failure, a People issue, or a Governance breakdown? Accurate diagnosis enables appropriate remediation.
The Model in Practice: Scenario Applications
Scenario 1: Ransomware Incident
A sophisticated ransomware attack encrypts critical systems. The immediate response focuses on Operations — containment, forensics, recovery. But the mental model prompts broader analysis across all six domains: why detection systems didn't identify the attack earlier; whether systems were properly hardened and backups implemented according to architectural specifications; whether the architecture enables adequate segmentation; whether resilience requirements align with business needs; whether the team has necessary incident response skills; and whether incident response procedures function as designed, with clear escalation paths.
This comprehensive analysis prevents narrow focus on immediate technical response whilst missing the systemic issues that enabled the attack.
Scenario 2: Board Presentation on Security Posture
A CISO must present security posture to the board. Without the mental model, the presentation might devolve into technical details incomprehensible to board members. With the model, focus shifts to Governance — how security integrates with enterprise risk management, what committees provide oversight, how compliance obligations are managed — and Strategy, emphasising how security investments align with business priorities and how resilience capabilities position the organisation. Technical details from Architecture, Engineering, and Operations are minimised unless specifically relevant to board decisions.
Scenario 3: Resource Allocation Decision
A CISO must allocate a £1 million budget increase across competing requests — new security tools, additional security engineers, an architecture review programme, security awareness training, and strategic planning capabilities. Without a mental model, the decision might default to the most vocal advocate or most recent pain point. With the model, systematic assessment across domains reveals that Operations and Engineering already receive substantial investment whilst Architecture reviews don't occur systematically, People development lags, and strategic planning capability remains immature. The model enables risk-informed allocation balancing immediate operational needs against longer-term capability development.
Organisational Benefits Beyond Individual Leadership
Common Language develops when teams use the model to create shared understanding of security leadership's scope. Discussions about capability gaps, priority-setting, and organisational development occur within a common framework rather than conflicting personal perspectives.
Institutional Knowledge becomes capturable. The model captures tacit knowledge that typically resides in experienced practitioners' heads. When CISOs depart, organisations lose this knowledge. The model enables transferring wisdom to successors and developing next-generation security leaders more systematically.
Maturity Assessment allows organisations to evaluate security capability maturity across domains, benchmarking against peers or tracking improvement over time. This provides evidence-based dialogue about security investments rather than resource allocation by squeaky wheel.
Scalability becomes possible as security organisations grow. The model provides structure for distributing leadership. Domain owners can develop expertise, make delegated decisions, and coordinate through understanding of inter-domain dependencies. This enables security functions to scale beyond what individual CISOs can manage directly.
Part VII: The Imperative for Structured Thinking in Security Leadership
Cognitive Limits and the Necessity of Frameworks
Human cognitive capacity imposes strict limits on unaided reasoning about complex systems. Working memory holds approximately seven chunks of information simultaneously. Complex problems involving dozens or hundreds of variables exceed this capacity by orders of magnitude.
Mental models provide cognitive scaffolding that expands effective reasoning capacity. Rather than holding all variables in working memory, leaders internalise frameworks that compress relationships into manageable structures. A skilled chess player doesn't evaluate millions of possible moves — they recognise patterns and apply strategic frameworks reducing the problem space to tractable dimensions.
The CISO role's multidimensional complexity exceeds unaided cognitive capacity. CISOs attempting to manage this complexity without structured frameworks inevitably experience attention capture, where urgent operational issues dominate at the expense of strategic capabilities; domain blindness, where familiar domains receive investment whilst unfamiliar ones deteriorate invisibly; reactive decision-making, where immediate pressures displace proactive capability building; and stakeholder misalignment, where the absence of a unifying framework renders it impossible to satisfy board, business units, and technical teams simultaneously.
The 21st Century Imperative
As digital transformation accelerates, security leadership complexity will intensify, not diminish. New technologies — artificial intelligence, quantum computing, ubiquitous IoT, cyber-physical systems — introduce novel security challenges. Geopolitical tensions manifest through cyberspace. Regulatory requirements multiply and sophisticate. Threat actors professionalise and industrialise.
In this context, structured mental models transition from helpful to essential. Security leaders operating without cognitive frameworks will increasingly struggle to maintain strategic perspective amidst operational chaos, build organisational capabilities matching the pace of technological change, communicate effectively across increasingly diverse stakeholder groups, make sound decisions under uncertainty with incomplete information, and develop successor security leaders inheriting accumulated wisdom.
The alternative to structured thinking isn't neutral — it's reactive, unsystematic thinking producing suboptimal outcomes.
Mental Models as Transferable Wisdom
Perhaps the most compelling case for mental models lies in knowledge transfer. Organisations invest years developing capable security leaders. When these leaders depart, their accumulated wisdom typically departs with them — locked in individual experience rather than captured in teachable form.
Mental models enable codifying tacit knowledge. The CISO Mental Model represents decades of security leadership experience compressed into structured framework. Aspiring security leaders can learn from this framework in months what would otherwise require years of direct experience. They avoid well-documented failure modes and apply proven approaches to common challenges.
This knowledge transfer serves individual career development and organisational resilience. Organisations developing security leaders using structured frameworks build bench strength, reduce succession risk, and create institutional memory surviving individual departures.
Conclusion: The Path Forward
The 21st century presents unprecedented complexity across every human endeavour. Digital transformation creates dependencies on cyber infrastructure few fully comprehend. Security leadership sits at the fulcrum of these dependencies, responsible for protecting the foundation enabling continued human progress whilst enabling the innovation and openness digital civilisation requires.
This leadership challenge exceeds human cognitive capacity without structured frameworks. Mental models provide the cognitive scaffolding enabling effective reasoning about overwhelming complexity.
The CISO Mental Model offers a structured framework purpose-built for modern security leadership. It decomposes multidimensional complexity into manageable domains whilst preserving understanding of critical interdependencies. It provides common language for organisational dialogue, structure for capability assessment and development, and framework for stakeholder communication. Most importantly, it codifies decades of practitioner wisdom into transferable form.
As digital transformation accelerates and cyber security's foundational importance intensifies, structured thinking evolves from competitive advantage to survival requirement. Security leaders employing robust mental models will navigate complexity more effectively, build stronger organisational capabilities, and deliver superior outcomes compared to those relying on unaided intuition.
The question isn't whether mental models matter — extensive evidence from cognitive science, organisational behaviour, and practitioner experience confirms they do. The question is whether security leaders will adopt effective models proactively or learn their necessity through avoidable failures.
The choice, and its consequences, remain ours to make.
